NetFlow to Monitor Network Traffic
NetFlow is a network protocol developed by Cisco Systems for collecting IP traffic information. NetFlow has become an industry standard for traffic monitoring and is supported on various platforms. Routers or switches that support NetFlow can collect IP traffic statistics on all interfaces where NetFlow is enabled, and later export those statistics as NetFlow records, towards at least one NetFlow collector.
To verify the top-talkers on the network, use the command,
Network Flows
A network flow can be defined in many ways. Cisco standard NetFlow defines a flow as a unidirectional sequence of packets that all share the following 7 values.
- Ingress interface (SNMP ifIndex)
- Source IP address
- Destination IP address
- IP protocol
- Source port for UDP or TCP, 0 for other protocols
- Destination port for UDP or TCP, type and code for ICMP, or 0 for other protocols
- IP Type of Service
Additional information added to a flow includes
- Flow timestamps to understand the life of a flow; timestamps are useful for calculating packets and bytes per second
- Next hop IP addresses including BGP routing Autonomous Systems (AS)
- Subnet mask for the source and destination addresses to calculate prefixes
- TCP flags to examine TCP handshakes
Configuration
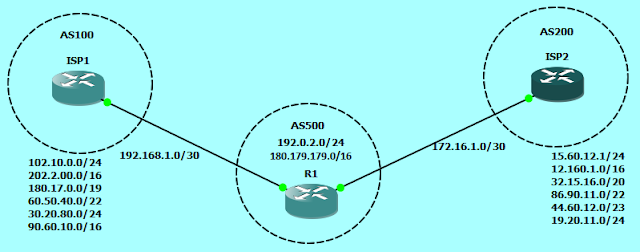
Netflow configuration on Cisco routers is very simple, just enable the NetFlow on interfaces, define the version to be used and the destination i.e. IP address of the NetFlow collector. In the below image, we will configure the router to send the flows to the workstation 192.168.100.20, where NetFlow Analyzer is installed.
Router#
interface FastEthernet 0/1
description ### INSIDE ###
ip address 192.168.100.1 255.255.255.0
ip flow ingress
!
ip flow-export version 9
ip flow-export destination 192.168.100.20 9996
Just this much configuration will start sending the Flows towards Netflow Analyzer. Here is the sample output for the LAN segment from the above scenario.
Apart from using the NetFlow collector, you can also use CLI to view the Flows using the command
show ip cache flow
NetFlow Top-Talkers
NetFlow top-talkers feature is also very handy to use from Command Line Interface when you want to identify users who are utilizing more WAN bandwidth. To configu-re flow-top-talkers, just add the following configuration to the above configuration on the Router.
ip flow-top-talkers
top 20
sort-by bytes
To verify the top-talkers on the network, use the command,
Router#sh ip flow top-talkers
SrcIf SrcIPaddress DstIf DstIPaddress Pr SrcP DstP Bytes
Fa0/1 192.168.100.12 Fa0/0 188.4.200.109 11 9215 7CB9 267K
Fa0/1 192.168.100.12 Fa0/0 122.150.182.223 11 9215 AF16 265K
Fa0/1 192.168.100.58 Fa0/0 50.140.2.134 06 D4FD C196 225K
Fa0/1 192.168.100.49 Fa0/0 74.125.236.133 06 C766 01BB 118K
Fa0/1 192.168.100.58 Fa0/0 41.158.32.28 11 81B7 82D7 107K
Fa0/1 192.168.100.58 Fa0/0 186.216.123.119 11 81B7 C8D3 97K
Fa0/1 192.168.100.12 Fa0/0 142.161.64.110 11 9215 B0BB 67K
Fa0/1 192.168.100.58 Fa0/0 105.236.42.243 11 81B7 C350 63K
Fa0/1 192.168.100.58 Fa0/0 68.41.128.72 11 81B7 D785 52K
Fa0/1 192.168.100.12 Fa0/0 124.179.75.73 11 9215 AC98 48K
Fa0/1 192.168.100.58 Fa0/0 83.39.147.222 11 81B7 0FA0 36K
Fa0/1 192.168.100.58 Fa0/0 77.126.153.4 11 81B7 DC90 34K
Fa0/1 192.168.100.58 Local 203.122.32.30 11 81B7 81B7 34K
Fa0/1 192.168.100.62 Fa0/0 205.209.161.108 06 CC11 4E21 18K
Fa0/1 192.168.100.58 Fa0/0 50.105.92.91 06 DDAA 836F 16K
Fa0/1 192.168.100.58 Fa0/0 115.64.185.87 11 81B7 B2B3 12K
Fa0/1 192.168.100.58 Fa0/0 62.57.156.182 11 81B7 434C 8851
Fa0/1 192.168.100.57 Fa0/0 74.125.236.150 06 C5F3 01BB 6174
Fa0/1 192.168.100.48 Fa0/0 137.135.131.132 06 F5DE 0050 5567
Fa0/1 192.168.100.58 Fa0/0 46.193.164.36 11 81B7 866D 5123
20 of 20 top talkers shown. 380 flows processed.







Comments
Post a Comment