NSX-T Configuration from Scratch
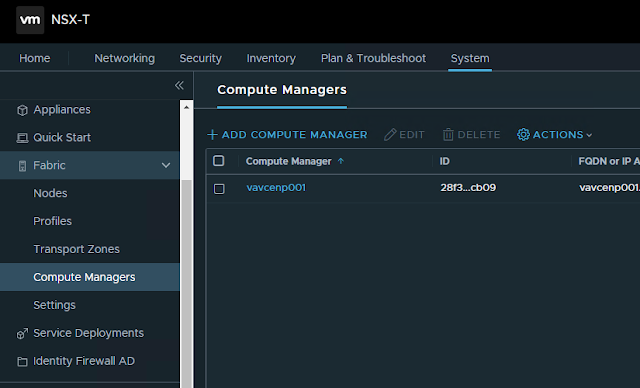
In this blog post we'll see step by step configuration of NSX-T 1. Add Compute Manager 2. Create Transport Zones as following a. One Overlay Transport Zone for Host and Edge Transport Nodes b. Two VLAN Transport Zones. One for Host Transport Nodes and another for Edge Transport Node. (having two separate VLAN transport zones is not necessary, a single VLAN Transport Zone can be used Host and Edge Transport zones) 3. Create Uplink profile for Host Transport Node In our design, we are using LAG consisting of two uplink on Host Transport Nodes. LAG is already created on vCenter ESXi hosts. Transport VLAN is the VLAN used for Host TEP IP address pool. There is no need to specify the MTU size in Host Uplink Profile, as we are using converged VDS in our design and MTU settings need to configured in VDS (on vCenter). MTU Settings on VDS 4. Create IP pool for Host Transport Nodes. In our case, we would be using DHCP. 5. Create Host Transport Node Profile Type: VDS (




