IKEv2 IPsec Site-to-Site VPN configuration on Cisco ASA 8.4(x)
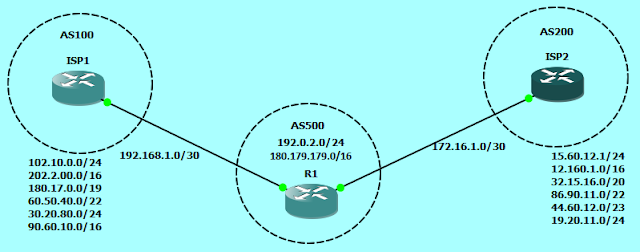
Though the crypto IKEv2 proposal command looks similar to the IKEv1 crypto isakmp policy command, there are many differences in how IKEv2 negotiates. Unlike IKEv1, the authentication method and SA lifetime are not negotiable in IKEv2, and they cannot be configured in the IKEv2 proposal. Also the IKEv2 proposal configuration supports specifying multiple options for each transform type and we can configure different pre-shared-key for local and remote authentication. Pseudo-Random Function (PRF) algorithm is the same as the integrity algorithm, and hence, it is not configured separately. Our goal is to configure site-to-site or l2l IKEv2 IPsec VPN between ASA1 and ASA2 which are running IOS 8.4(2). IP addressing scheme is mentioned in the network diagram.
ASA2# sh crypto ikev2 sa detail
IKEv2 SAs:
Session-id:1, Status:UP-ACTIVE, IKE count:1, CHILD count:1
Tunnel-id Local Remote Status Role
9617881 190.1.1.2/500 180.1.1.2/500 READY RESPONDER
Encr: AES-CBC, keysize: 256, Hash: SHA256, DH Grp:2, Auth sign: PSK, Auth verify: PSK
Life/Active Time: 86400/186 sec
Session-id: 1
Status Description: Negotiation done
Local spi: 1D72FACA014E0232 Remote spi: 85A271A5A90EBC64
Local id: 190.1.1.2
Remote id: 180.1.1.2
Local req mess id: 6 Remote req mess id: 8
Local next mess id: 6 Remote next mess id: 8
Local req queued: 6 Remote req queued: 8
Local window: 1 Remote window: 1
DPD configured for 10 seconds, retry 2
NAT-T is not detected
Child sa: local selector 192.168.0.0/0 - 192.168.3.255/65535
remote selector 172.16.0.0/0 - 172.16.3.255/65535
ESP spi in/out: 0x351a8276/0x31d76ed6
AH spi in/out: 0x0/0x0
CPI in/out: 0x0/0x0
Encr: AES-CBC, keysize: 256, esp_hmac: SHA96
ah_hmac: None, comp: IPCOMP_NONE, mode tunnel
ASA1
interface GigabitEthernet1
nameif OUTSIDE
security-level 0
ip address 180.1.1.2 255.255.255.252
!
interface GigabitEthernet2
nameif INSIDE
security-level 100
ip address 172.16.0.2 255.255.255.0
!
access-list VPN extended permit ip 172.16.0.0 255.255.252.0 192.168.0.0 255.255.252.0
!
crypto ipsec ikev2 ipsec-proposal VPNPRPSL
protocol esp encryption aes-256
protocol esp integrity sha-1
crypto map VPNMAP 1 match address VPN
crypto map VPNMAP 1 set peer 190.1.1.2
crypto map VPNMAP 1 set ikev2 ipsec-proposal VPNPRPSL
crypto map VPNMAP interface OUTSIDE
crypto ikev2 policy 1
encryption aes-256
integrity sha256
group 2
prf sha
lifetime seconds 86400
crypto ikev2 enable OUTSIDE
!
tunnel-group 190.1.1.2 type ipsec-l2l
tunnel-group 190.1.1.2 ipsec-attributes
ikev2 remote-authentication pre-shared-key cisco
ikev2 local-authentication pre-shared-key cisco123
ASA2
interface GigabitEthernet1
nameif OUTSIDE
security-level 0
ip address 190.1.1.2 255.255.255.252
!
interface GigabitEthernet2
nameif INSIDE
security-level 100
ip address 192.168.0.2 255.255.255.0!access-list VPN extended permit ip 192.168.0.0 255.255.252.0 172.16.0.0 255.255.252.0
!
crypto ipsec ikev2 ipsec-proposal VPNPRPSL
protocol esp encryption aes-256
protocol esp integrity sha-1
crypto map VPNMAP 1 match address VPN
crypto map VPNMAP 1 set peer 180.1.1.2
crypto map VPNMAP 1 set ikev2 ipsec-proposal VPNPRPSL
crypto map VPNMAP interface OUTSIDE
crypto ikev2 policy 1
encryption aes-256
integrity sha256
group 2
prf sha
lifetime seconds 86400
crypto ikev2 enable OUTSIDE
!
tunnel-group 180.1.1.2 type ipsec-l2l
tunnel-group 180.1.1.2 ipsec-attributes
ikev2 remote-authentication pre-shared-key cisco123
ikev2 local-authentication pre-shared-key cisco
ASA2# sh crypto ikev2 sa detail
IKEv2 SAs:
Session-id:1, Status:UP-ACTIVE, IKE count:1, CHILD count:1
Tunnel-id Local Remote Status Role
9617881 190.1.1.2/500 180.1.1.2/500 READY RESPONDER
Encr: AES-CBC, keysize: 256, Hash: SHA256, DH Grp:2, Auth sign: PSK, Auth verify: PSK
Life/Active Time: 86400/186 sec
Session-id: 1
Status Description: Negotiation done
Local spi: 1D72FACA014E0232 Remote spi: 85A271A5A90EBC64
Local id: 190.1.1.2
Remote id: 180.1.1.2
Local req mess id: 6 Remote req mess id: 8
Local next mess id: 6 Remote next mess id: 8
Local req queued: 6 Remote req queued: 8
Local window: 1 Remote window: 1
DPD configured for 10 seconds, retry 2
NAT-T is not detected
Child sa: local selector 192.168.0.0/0 - 192.168.3.255/65535
remote selector 172.16.0.0/0 - 172.16.3.255/65535
ESP spi in/out: 0x351a8276/0x31d76ed6
AH spi in/out: 0x0/0x0
CPI in/out: 0x0/0x0
Encr: AES-CBC, keysize: 256, esp_hmac: SHA96
ah_hmac: None, comp: IPCOMP_NONE, mode tunnel




its very helpful... Thanks...
ReplyDeletenice
ReplyDelete